The phishing story
What Sally did…
When Sally was reading her emails one morning, she noticed an email from the IT department asking her to confirm her username and password, so that they knew her account was still being used. The email said that if Sally did not respond with her username and password, her account would be deleted. Sally panicked and worried about losing all her work emails, so responded with her username and password immediately.
The consequence
Sally’s account was used to send out 1000s of spam emails, which generated 1000s of undeliverable emails to Sally’s email account. This caused an awful lot trouble for both the IT staff and Sally.
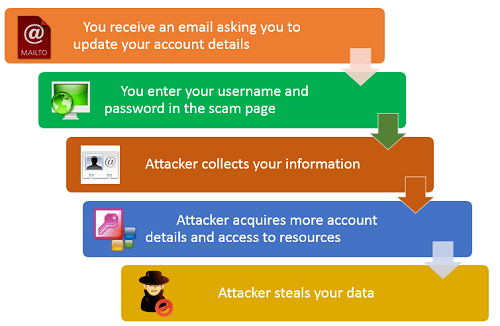
How does phishing work?
Phishing emails – how they make you feel
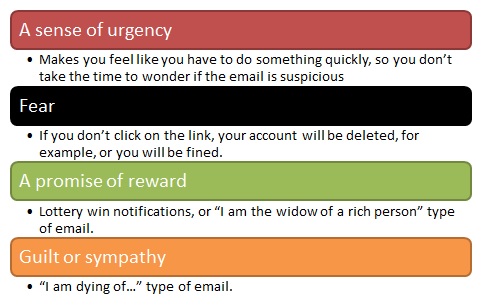
The main aim of a phishing email is to separate you from your money or your private information.
To do this, they use the following:
Combine them, and you are sorted: “I am the dying widow of XXX, who has loads of money and needs to get it out of the country before next Tuesday”.
So if an email makes you feel: guilty, panicky, afraid, or greedy, stop and ask yourself why. It’s probably a phishing email.
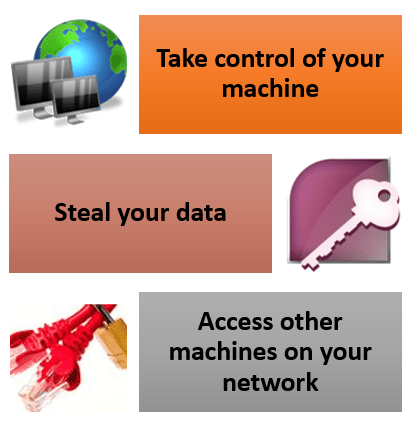
If you had clicked on the link…
Your computer would have downloaded a malicious ZIP file named “Internal_Discussion_Project.zip”. This file contained a malicious program that installs a backdoor – a backdoor is software that allows an intruder to send commands to the computer remotely.
The consequence…
Backdoors can allow the attacker to:
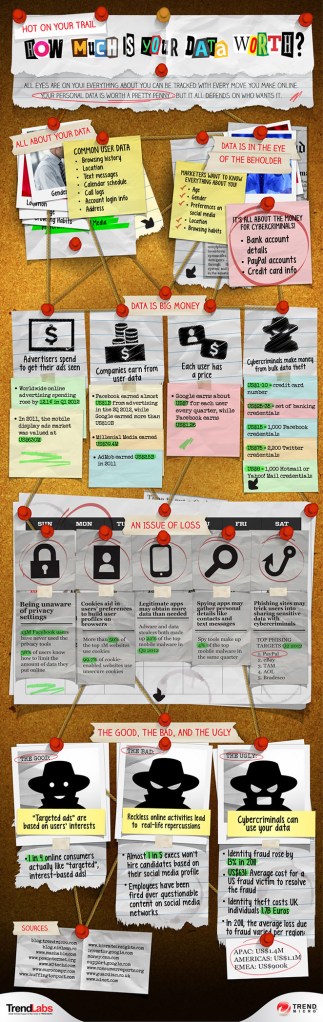
How much is your data worth?
The following infographic from TrendMicro illustrates why it’s critical that you keep your personal information and the personal information of others safe:
Spear phishing
These emails:
- target a specific individual or organization
- seek unauthorized access to confidential data
How do you recognise a spear phishing email?
Check for these signs:
- The email contains a malicious attachment
- The email contains a hyperlink to a malicious file
- The subject line and email text are usually relevant to the recipient
- Webmail accounts using real people’s names are used to send the emails – e.g. a colleague, head of department, IT support person
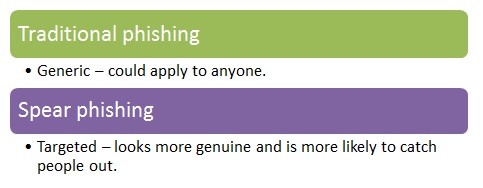
Main differences between traditional and spear phishing:
The important thing to remember is that, as spear phishing is targeted, it’s likely to steal more valuable information about you and/or your organisation.
Social engineering
It is important to be aware that you can be tricked into giving out information in many different ways. Be vigilant when being asked for information over email, over the phone, and in person.
Be aware that information about yourself that you make public on the Internet can be used to trick you into giving out information. If someone calls you for information, but already knows some of it, you are more likely to give them the information. That’s why it is important not to give out information, as even something that seems small can be put together with other things to produce something significant. Have a look at the video below for a good example…